[ad_1]
Our earlier weblog put up, Designing and Deploying Cisco AI Spoofing Detection, Half 1: From Machine to Behavioral Mannequin, launched a hybrid cloud/on-premises service that detects spoofing assaults utilizing behavioral site visitors fashions of endpoints. In that put up, we mentioned the motivation and the necessity for this service and the scope of its operation. We then offered an outline of our Machine Studying growth and upkeep course of. This put up will element the worldwide structure of Cisco AISD, the mode of operation, and the way IT incorporates the outcomes into its safety workflow.
Since Cisco AISD is a safety product, minimizing detection delay is of great significance. With that in thoughts, a number of infrastructure selections had been designed into the service. Most Cisco AI Analytics companies use Spark as a processing engine. Nonetheless, in Cisco AISD, we use an AWS Lambda perform as an alternative of Spark as a result of the warmup time of a Lambda perform is often shorter, enabling a faster era of outcomes and, subsequently a shorter detection delay. Whereas this design alternative reduces the computational capability of the method, that has not been an issue due to a custom-made caching technique that reduces processing to solely new information on every Lambda execution.
International AI Spoofing Detection Structure Overview
Cisco AISD is deployed on a Cisco DNA Middle community controller utilizing a hybrid structure of an on-premises controller tethered to a cloud service. The service consists of on-premises processes in addition to cloud-based parts.
The on-premises parts on the Cisco DNA Middle controller carry out a number of very important capabilities. On the outbound information path, the service frequently receives and processes uncooked information captured from community gadgets, anonymizes buyer PII, and exports it to cloud processes over a safe channel. On the inbound information path, it receives any new endpoint spoofing alerts generated by the Machine Studying algorithms within the cloud, deanonymizes any related buyer PII, and triggers any Adjustments of Authorization (CoA) through Cisco Identification Companies Engine (ISE) on affected endpoints.
The cloud parts carry out a number of key capabilities centered totally on processing the excessive quantity information flowing from all on-premises deployments and working Machine Studying inference. Particularly, the analysis and detection mechanism has three steps:
- Apache Airflow is the underlying orchestrator and scheduler to provoke compute capabilities. An Airflow DAG often enqueues computation requests for every energetic buyer to a queuing service.
- As every computation request is dequeued, a corresponding serverless compute perform is invoked. Utilizing serverless capabilities permits us to regulate compute prices at scale. It is a extremely environment friendly multi-step, compute-intensive, short-running perform that performs an ETL step by studying uncooked anonymized buyer information from information buckets and remodeling them right into a set of enter function vectors for use for inference by our Machine Studying fashions for spoof detection. This compute perform leverages a few of cloud suppliers’ widespread Operate as a Service structure.
- This perform then additionally performs the mannequin inference step on the function vectors produced within the earlier step, finally resulting in the detection of spoofing makes an attempt if they’re current. If a spoof try is detected, the small print of the discovering are pushed to a database that’s queried by the on-premises parts of Cisco DNA Middle and at last offered to directors for motion.
Determine 1 captures a high-level view of the Cisco AISD parts. Two parts, particularly, are central to the cloud inferencing performance: the Scheduler and the serverless capabilities.
The Scheduler is an Airflow Directed Acyclic Graph (DAG) chargeable for triggering the serverless perform executions on energetic Cisco AISD buyer information. The DAG runs at high-frequency intervals pushing occasions right into a queue and triggering the inference perform executions. The DAG executions put together all of the metadata for the compute perform. This contains figuring out clients with energetic flows, grouping compute batches based mostly on telemetry quantity, optimizing the compute course of, and many others. The inferencing perform performs ETL operations, mannequin inference, detection, and storage of spoofing alerts if any. This compute-intensive course of implements a lot of the intelligence for spoof detection. As our ML fashions get retrained frequently, this structure permits the fast rollout—or rollback if wanted—of up to date fashions with none change or influence on the service.
The inference perform executions have a steady common runtime of roughly 9 seconds, as proven in Determine 2, which, as stipulated within the design, doesn’t introduce any important delay in detecting spoofing makes an attempt.

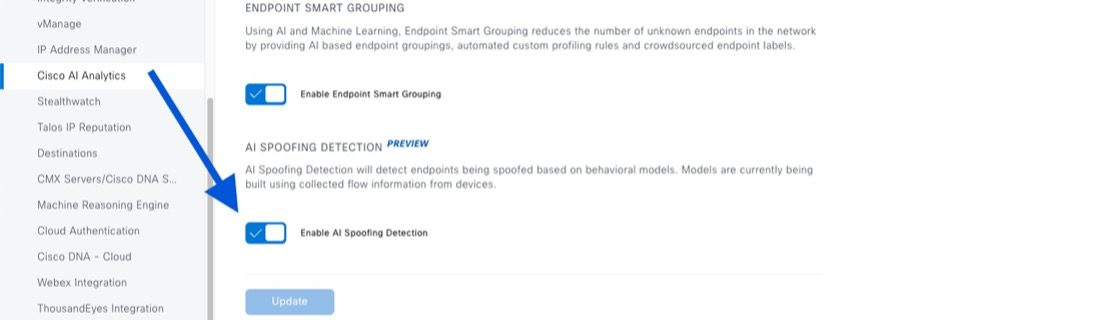
Cisco AI Spoofing Detection in Motion
On this weblog put up sequence, we described the inner design ideas and processes of the Cisco AI Spoofing Detection service. Nonetheless, from a community operator’s perspective, all these internals are fully clear. To start out utilizing the hybrid on-premises/cloud-based spoofing detection system, Cisco DNA Middle Admins have to allow the corresponding service and cloud information export in Cisco DNA Middle System Settings for AI Analytics, as proven in Determine 3.
As soon as enabled, the on-prem part within the Cisco DNA Middle begins to export related information to the cloud that hosts the spoof detection service. The cloud parts robotically begin the method for scheduling the mannequin inference perform runs, evaluating the ML spoofing detection fashions in opposition to incoming site visitors, and elevating alerts when spoofing makes an attempt on a buyer endpoint are detected. When the system detects spoofing, the Cisco DNA Middle within the buyer’s community receives an alert with data. An instance of such a detection is proven in Determine 4. Within the Cisco DNA Middle console, the community operator can set choices to execute pre-defined containment actions for the endpoints marked as spoofed: shut down the port, flap the port, or re-authenticate the port from reminiscence.
Share:
[ad_2]