[ad_1]
Cybersecurity assaults complication and damaging impression are at all times holding SOC analyst at their edge. Prolonged Detection and Response (XDR) options are likely to simplify for Sam, a SOC analyst, his job by simplifying the workflow and course of that contain the lifecycle of a menace investigation from detection to response. On this submit we are going to discover how SecureX, Safe Cloud Analytics (NDR), Safe Endpoint (EDR) with their seamless integration speed up the power to realize XDR outcomes.
Significant incidents
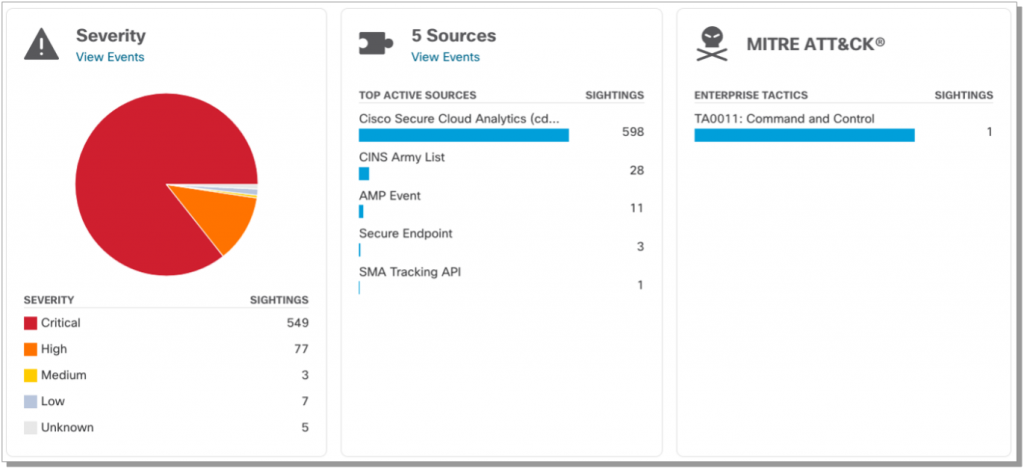
One of many first challenges for Sam is alert fatigue. With the overwhelming variety of alerts coming from a number of sources and the shortage of relevance or correlation, decreases the worth of those alerts to the purpose that they develop into as meaningless as having none. To counter this impact, Cisco Safe Cloud Analytics and Cisco Safe Endpoint restrict alert promotion to SecureX to solely embody excessive constancy alerts with vital severity and marking them as Excessive Affect incidents inside SecureX Incident supervisor.

This functionality reduces the noise coming from the supply, whereas holding the opposite alerts obtainable for investigation, placing impactful incidents on the prime of Sam’s to do listing. Now, Sam is assured that his time is spent in a prioritized method and helps guarantee he’s tackling a very powerful threats first. Computerized incident provisioning accelerates incident response by bringing give attention to probably the most impactful incidents.
Priceless enrichment
Understanding the mechanics and knowledge round a particular incident is a key issue for Remi, an incident responder, in his day-to-day work. Reaching his duties precisely is tightly coupled along with his capacity to scope and perceive the impression of an incident and to assemble all doable knowledge from the setting which will be related to an incident together with units, customers, recordsdata hashes, e-mail ids, domains IPs and others. SecureX Incident Supervisor’s automated enrichment functionality completes this knowledge assortment for top impression incidents mechanically. The information is then categorised into targets, observables, and indicators and added to the incident to assist the analyst higher perceive the incident’s scope and potential impression.

The Incident Supervisor and automated enrichment gives Remi with essential info such because the related MITRE Techniques and Strategies utilized throughout this incident, the contributing menace vectors, and safety options. As well as, the Incident Supervisor aggregates occasions from a number of sources into the identical excessive impression incident that the enrichment was triggered on future offering Remi with extra very important context.
This automated enrichment for top impression incidents is important to Remi’s understanding as a lot as doable about an incident because it happens and considerably accelerates him figuring out the right response for the menace. This brings us to the following step in our incident detection to response workflow.
Quicker response and investigations
It is necessary for an XDR to correlate the proper info for the Safety Analyst and incident responder to know an assault however it’s equally vital to supply an efficient response mechanism. That is precisely what SecureX gives with the power to use a response to an observable with a easy a single click on or by way of automation.
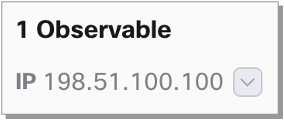
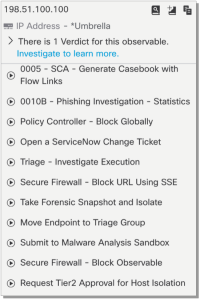
These workflows will be invoked to dam a website, IP or URL throughout a full setting with a easy click on, leveraging present integrations akin to firewalls or umbrella and others. Workflows will be made obtainable to the menace response pivot menu the place they’re helpful for performing particular host particular actions, akin to isolate a number, take a number snapshot, and extra.
Along with response workflows, the pivot menu gives the power to leverage Safe Cloud Analytics (SCA) telemetry by producing a case ebook linking again to telemetry searches inside SCA. This automation is vital to understanding the unfold of a menace throughout an setting. An excellent instance on this, is figuring out all hosts speaking to a command-and-control vacation spot earlier than this vacation spot was recognized as malicious. This can be a pre-existing SecureX workflow which will be taken benefit of at present see workflow 0005 – SCA – Generate Case ebook with Circulation Hyperlinks.

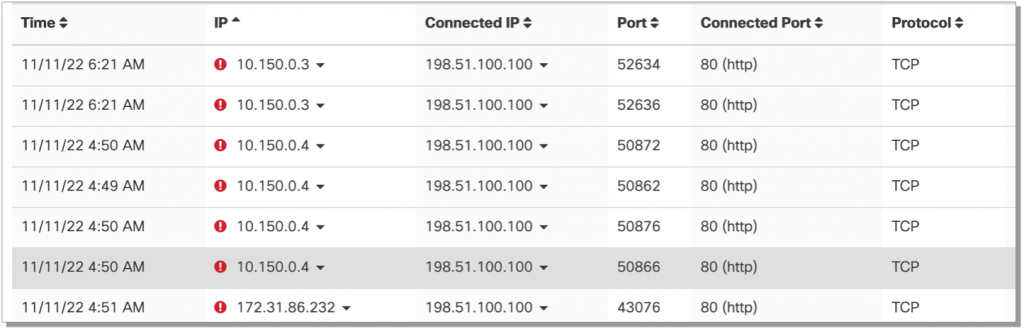
Automating responses
Decreasing time to remediation is a key side of holding a enterprise safe, SecureX orchestration automates responses with varied options specifically with NDR detections from SCA and use observables from these alerts to isolate hosts leveraging Safe Endpoint. SCA can ship alerts through Webhooks and SecureX Orchestration obtain them as triggers to launch an NDR- EDR workflow to isolate hosts mechanically. (0014-SCA-Isolate endpoints from alerts)
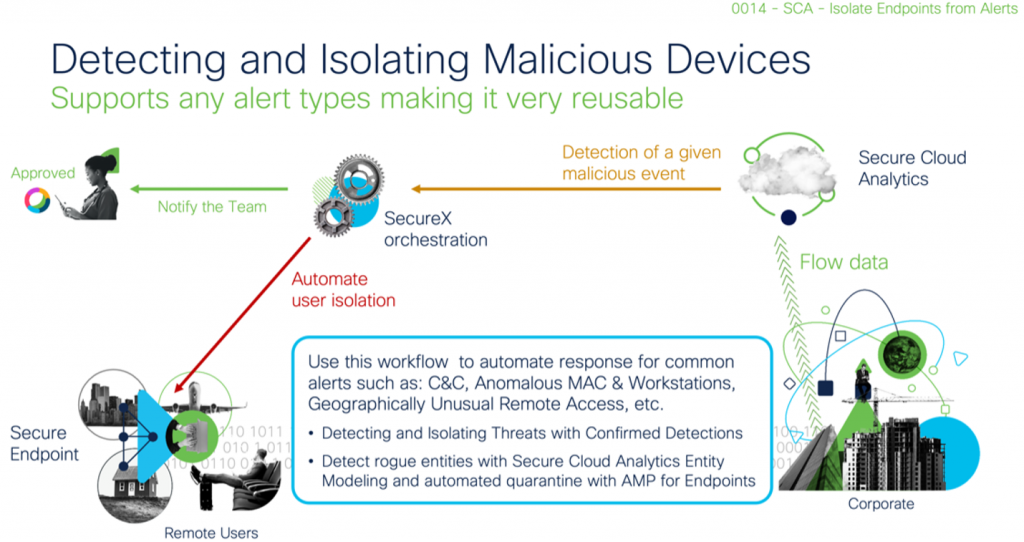
This orchestration workflow mechanically isolates rogue units in a community or comprise confirmed menace alerts acquired from Cisco’s Machine studying menace detection cloud and can be utilized for a number of totally different response eventualities.
The facility of automation introduced by SecureX, Safe Cloud Analytics and Safe Endpoint accelerates XDR outcomes drastically which simplifies Safety Analyst (Sam) and Incident Responder (Remi) jobs and make it extra environment friendly with correct incident prioritization, automated investigation/enrichment and most significantly automating responses.
We’d love to listen to what you assume. Ask a Query, Remark Beneath, and Keep Linked with Cisco Safe on social!
Cisco Safe Social Channels
Share:
[ad_2]